ScopSign™
Document Security Solution: Validation, Electronic Signature…


Document and Process Security
Key Functions: ScopSign
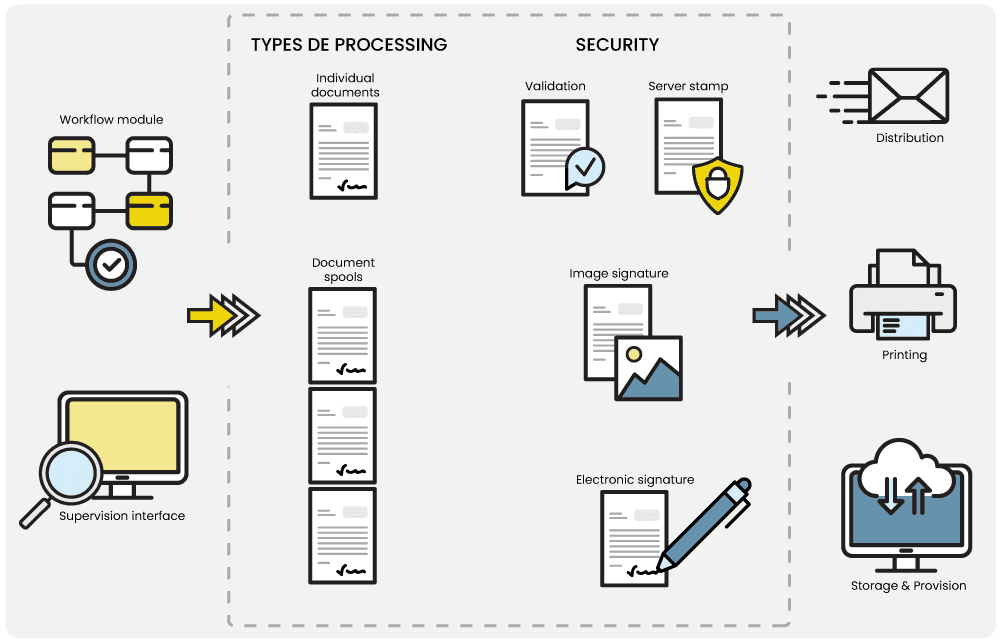
Various Security Levels
ScopSign offers different levels of security within the company’s business processes. From the simple validation of a document to an electronic signature, it’s possible to bring value to documents and workflows.
Individual Documents or Spool Documents?
ScopSign works directly on all documents: whether they are single documents manually generated or document spools generated by the user’s different information systems, ScopSign is able to handle these flows and process them.
At the Heart of the Scop Software Suite™
ScopSign is perfectly integrated into the Scop Software Suite by offering security possibilities to each application. For example, it is possible for a user to validate a mail to his superior in the ScopHybrid solution, or to electronically archive one’s most important documents in the EDM solution ScopMaster+.
Workflow Creation
The workflow module present in ScopSign proposes an administration interface for the implementation of security workflows. The module allows the definition of one or more security or sending steps, cumulative or not. These possibilities answer the business problems and the different wishes of the users.

Want to discover more information about ScopSign?
Discover the Functionalities of ScopSign
- Compatibility with all information systems and easy integration into all publishing chains.
- A solution completely integrated within the Scop Software Suite™: easy connection with ScopHybrid...
- Multiple possibilities to secure documents: validation, image signature, electronic signature, server seal…
- A supervision interface allows the administrator or a superior to visualize all the actions he or she has to perform.
- Sending documents to solutions of the Scop Software™ to archive or send.
Example of use: to countersign an important document that must be sent urgently. Once signed, the document is directed to an email server to send and archived in parallel in the ScopMaster+ EDM/ECM solution. - A powerful workflow that can use several validation and signature possibilities… one after the other.
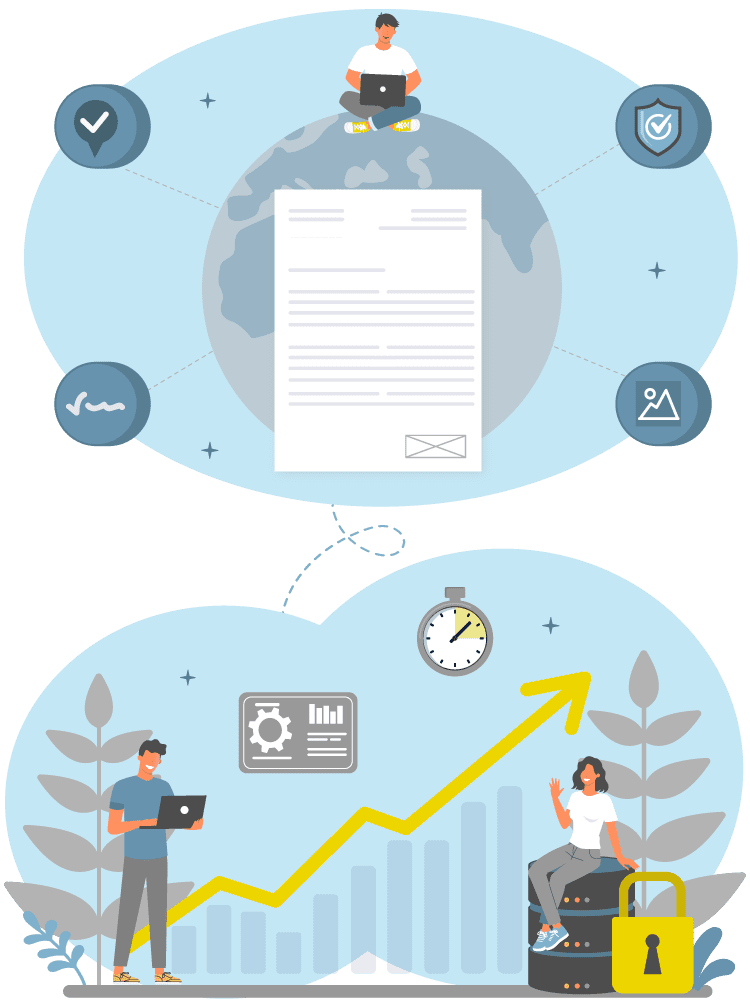
- Accessibility to ScopSign is available via PC, tablet, or Smartphone. So documents can be signed or validated anywhere.
In France, the rate of document fraud is estimated at between 3 and 6%. The use of solutions to guarantee the integrity and durability of documents is essential.
ScopSign: Benefits
Secure the Most Important Documents
ScopSign brings value to the most important documents. Depending on the level of criticality. The different levels of security bring a strong guarantee to the company, the employees, and the recipients. Security technologies respect the legal standards of security, integrity, and durability.
Reducing Expenses
30% of employees admit that they often print a document and throw it away a few minutes later, especially in a print-signature-scan context. A document signed directly online reduces printing costs and the time spent on these administrative tasks.
A Global Solution
ScopSign interfaces with ScopHybrid mail creation and sending solutions to allow, for example, the validation of a third person with an image signature before sending an important mail.
With the ScopSubmit sending portal, it’s possible to deposit a file to be returned signed. The solution can even manage a file with multiple pages to be signed. The file is then divided and each document can be signed individually.